Shared Directory
By Narcissus
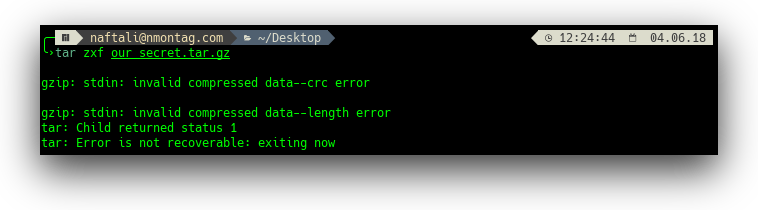
We downloaded and extracted win.zip and got a file called our_secret.tar.gz. When trying to extract it we get an error:
We notice that there are some randomly capitalized letters in the challenge description CRLF which is the windows line endings. Using file command we check what line endings the tar has:
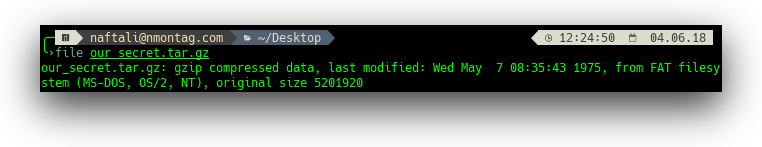
Indeed we see it's using DOS line endings, so maybe we need to convert them to unix ones?
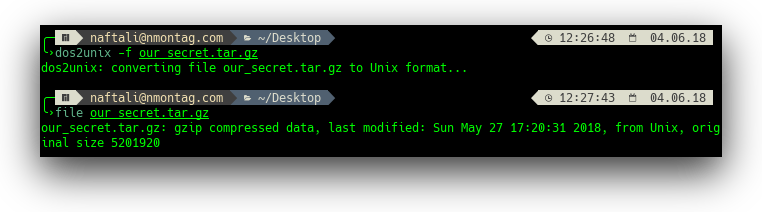
We successfully converted the files line endings, and now extracting gives us a folder named out with 4999 files in it and another file named model.json.
Looking at the file we see that it's header mentions something called FemtoZip. Following the official instructions we built the program and ran it with the following command ./fzip --model ~/model.json --decompress ~/out (those of you paying close attention will notice that the file locations don't add up with the previous steps, that is because I had to use a different computer for this stage).
All the files inside out became readeable. We combined them into 1 file string * > strings and got a long file containing a bunch of json values.
We noticed the string BSidesTLV appeared 2503 times while the string BSidesTLV{ImNotTheFlag} appeared only 2502 times, so we deleted all occurrences of the latter.
We now could easily find the correct flag: BSidesTLV{F3mZ1pisTh3B3st}

