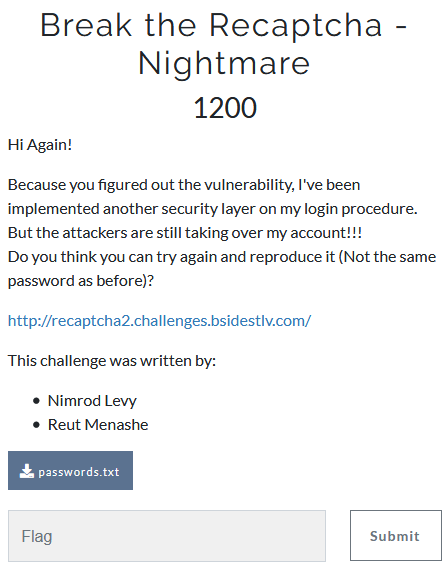
Break the Recaptcha - Nightmare
- Category: Web Application
- 1200 Points
- Solved by the JCTF Team
Description
Solution
This challenge is very similar to the previous 'Break the Recaptcha' challenge, with a little twist.
In this case, after trying to log in incorrectly for 3 times, the server would reply with 'Your IP Address has been locked for one hour!', even when we 'spoofed' the captcha correctly.
This simple brute-force protection meant that we could no longer use the previous solution, as 3 attempts per hour would simply take too long.
After a few unsuccessful attempts to find a flaw in the brute-force protection (such as spoofing the X-Forwarded-For header) we decided we truly need to attempt the logins from unique IP addresses.
For this we dumped a large list of free http proxies, and added the following code to the requests logic:
proxy_list = list(set(open('ProxyList.txt', 'rb').readlines()))
proxies = {'http': random.choice(proxy_list)}
try:
s.get('http://recaptcha2.challenges.bsidestlv.com/', headers=headers, proxies=proxies, timeout=4)
...
except Exception:
retry_logic_hereThis means each login attempt was performed using a different http proxy, and thus the challenge server saw it coming from a different IP address.
Note that we also added a timeout and an error handling mechanism, as many of these proxies are not very reliable.
