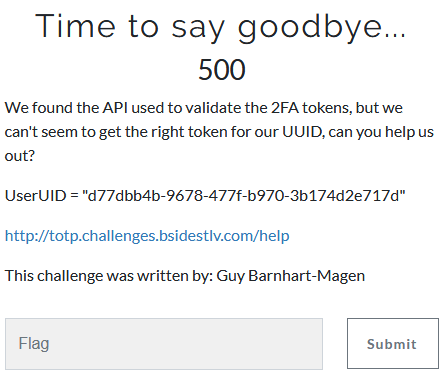
Time to say goodbye...
- Category: Cryptography
- 500 Points
- Solved by the JCTF Team
Description
Solution
In this challenge, 2 APIs in addition to the “help”:
/getuuid to "Generate a valid UUID in the system"
/validate/{uuid}:{token} to "Validate a given token for a UUID"
“getuuid”, in the 2nd version of this problem, was returning some UUID with a valid 6 digits token.
The goal is to use the “validate” API with the given UserUID with a valid token.
An invalid token return an error with the time, in the form: int(time.time())
Sending a uuid and token, in the same second it was requested from the server, to the validate API returned a success message (but not the flag, since it was not the right UserUUID.
The best hint would have been to forget anything you know about TOTP, hash functions, real 2FA, or in fact, security at all.
The solution consisted of xor-ing the time with the last digits of the UUID, after truncations and modulo to 6 chars, at each steps:
***(int(UserUUID[-6:],16) % 1000000) ^ (int(time.time()) % 1000000)[-6:]***That was all. Next challenge please.
